华为AC6605无线控制器MAC地址认证全流程实战指南
在企业无线网络环境中,MAC地址认证作为一种轻量级接入控制方案,既能提供基础安全防护,又能实现无感知的用户体验。本文将深入解析华为AC6605控制器上MAC地址认证的完整实施流程,涵盖本地认证与RADIUS服务器对接两种模式,并分享实际部署中的高阶技巧与排错方法。
1. 基础环境准备与AP上线
1.1 网络拓扑规划
典型的企业WLAN部署采用三层组网架构:
- 接入层:AP设备通过PoE交换机接入
- 汇聚层:AC控制器部署于此,管理AP和终端接入
- 核心层:连接RADIUS服务器和互联网出口
建议划分三个基础VLAN:
- 管理VLAN:用于AC与AP间通信(建议VLAN 100)
- 业务VLAN:终端用户数据转发(建议VLAN 101)
- 服务VLAN:连接RADIUS服务器(建议VLAN 102)
1.2 基础网络配置
# 启用DHCP服务
[AC6605] dhcp enable
# 配置管理VLAN接口
[AC6605] interface Vlanif 100
[AC6605-Vlanif100] ip address 192.168.100.1 24
[AC6605-Vlanif100] dhcp select interface
[AC6605-Vlanif100] quit
# 配置上行接口
[AC6605] interface GigabitEthernet 0/0/1
[AC6605-GigabitEthernet0/0/1] port link-type trunk
[AC6605-GigabitEthernet0/0/1] port trunk allow-pass vlan 100 101
[AC6605-GigabitEthernet0/0/1] quit
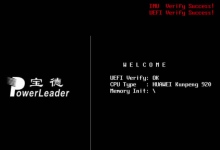
1.3 AP上线配置关键步骤
# 配置CAPWAP源接口
[AC6605] capwap source interface Vlanif 100
# 创建AP组
[AC6605] wlan
[AC6605-wlan-view] ap-group name office
[AC6605-wlan-ap-group-office] quit
# 离线添加AP(MAC认证模式)
[AC6605-wlan-view] ap auth-mode mac-auth
[AC6605-wlan-view] ap-id 1 ap-mac 60de-4476-e360
[AC6605-wlan-ap-1] ap-name meeting-room
[AC6605-wlan-ap-1] ap-group office
[AC6605-wlan-ap-1] quit
提示:AP上线后可通过display ap all查看状态,当State显示为"nor"表示正常上线。
2. MAC地址认证本地配置方案
2.1 认证基础架构搭建
本地认证适合终端数量少(<50)的场景,配置流程如下:
[AC6605-wlan-view] security-profile name mac-auth-local
[AC6605-wlan-sec-prof-mac-auth-local] security open
[AC6605-wlan-sec-prof-mac-auth-local] quit
[AC6605-wlan-view] ssid-profile name employee
[AC6605-wlan-ssid-prof-employee] ssid HUAWEI-EMP
[AC6605-wlan-ssid-prof-employee] quit
2.2 MAC认证核心配置
# 启用全局MAC认证
[AC6605] mac-authen
# 创建WLAN-ESS接口并启用MAC认证
[AC6605] interface Wlan-Ess 1
[AC6605-Wlan-Ess1] mac-authentication enable
[AC6605-Wlan-Ess1] quit
# 本地用户添加(MAC地址作为用户名)
[AC6605] aaa
[AC6605-aaa] local-user 5489-9828-3f0e password cipher 5489-9828-3f0e
[AC6605-aaa] local-user 5489-9828-3f0e service-type 8021x
[AC6605-aaa] quit
2.3 服务集绑定与验证
# 创建VAP模板
[AC6605-wlan-view] vap-profile name emp-vap
[AC6605-wlan-vap-prof-emp-vap] forward-mode direct-forward
[AC6605-wlan-vap-prof-emp-vap] service-vlan 101
[AC6605-wlan-vap-prof-emp-vap] security-profile mac-auth-local
[AC6605-wlan-vap-prof-emp-vap] ssid-profile employee
[AC6605-wlan-vap-prof-emp-vap] wlan-ess 1
[AC6605-wlan-vap-prof-emp-vap] quit
# 绑定到AP射频
[AC6605-wlan-view] ap 1 radio 0
[AC6605-wlan-radio-1/0] vap-profile emp-vap wlan 1
[AC6605-wlan-radio-1/0] quit
# 提交配置
[AC6605-wlan-view] commit all
验证命令:
display mac-authen user # 查看已认证用户
display access-user auth-type mac # 查看MAC认证用户详情
3. RADIUS服务器对接方案
3.1 RADIUS服务器配置要点
以FreeRADIUS为例,需配置clients.conf和users文件:
# /etc/freeradius/3.0/clients.conf
client 192.168.100.1 {
secret = Huawei@123
shortname = AC6605
}
# /etc/freeradius/3.0/users
"5489-9828-3f0e" Cleartext-Password := "5489-9828-3f0e"
Tunnel-Type = VLAN,
Tunnel-Medium-Type = IEEE-802,
Tunnel-Private-Group-ID = 101
3.2 AC端RADIUS配置
# 创建RADIUS服务器模板
[AC6605] radius-server template radius1
[AC6605-radius-radius1] radius-server authentication 192.168.102.100 1812
[AC6605-radius-radius1] radius-server shared-key cipher Huawei@123
[AC6605-radius-radius1] undo radius-server user-name domain-included
[AC6605-radius-radius1] quit
# 配置AAA认证方案
[AC6605] aaa
[AC6605-aaa] authentication-scheme radius-mac
[AC6605-aaa-authen-radius-mac] authentication-mode radius
[AC6605-aaa-authen-radius-mac] quit
# 创建域并绑定方案
[AC6605-aaa] domain huawei.com
[AC6605-aaa-domain-huawei.com] authentication-scheme radius-mac
[AC6605-aaa-domain-huawei.com] radius-server radius1
[AC6605-aaa-domain-huawei.com] quit
[AC6605-aaa] quit
# 修改WLAN-ESS接口配置
[AC6605] interface Wlan-Ess 1
[AC6605-Wlan-Ess1] force-domain huawei.com
[AC6605-Wlan-Ess1] quit
3.3 认证流程优化参数
| 超时时间 | 15s | radius-server timer response-timeout 15 |
| 重试次数 | 3次 | radius-server retry 3 |
| 实时计费间隔 | 15分钟 | accounting interim interval 900 |
| NAS-ID | 按位置设置 | radius-server nas-id Floor1-AC |
4. 高级运维与排错技巧
4.1 批量导入MAC地址
使用Python脚本实现MAC地址批量导入:
import sys
from netmiko import ConnectHandler
ac6605 = {
'device_type': 'huawei',
'host': '192.168.100.1',
'username': 'admin',
'password': 'Admin@123',
}
mac_list = ['5489-9828-3f0e', '60de-4476-e360'] # 从Excel导入的MAC列表
conn = ConnectHandler(**ac6605)
config_commands = ['aaa']
for mac in mac_list:
config_commands.append(f'local-user {mac} password cipher {mac}')
config_commands.append(f'local-user {mac} service-type 8021x')
config_commands.append('return')
output = conn.send_config_set(config_commands)
print(output)
conn.disconnect()
4.2 常见故障排查表
| AP无法上线 | CAPWAP隧道建立失败 | display capwap configuration |
| MAC认证失败 | 用户名格式错误 | display mac-authen failed-user |
| RADIUS无响应 | 网络连通性问题 | ping 192.168.102.100 |
| 认证超时 | 共享密钥不匹配 | display radius-server configuration |
4.3 Wireshark抓包分析
关键过滤条件:
capwap || eap || radius # 捕获认证协议流量
http.request.uri contains "portal" # 捕获Portal重定向
典型CAPWAP隧道建立过程:
在RADIUS认证过程中,重点关注Access-Request/Access-Accept报文中的属性:
- Calling-Station-ID:携带终端MAC地址
- NAS-IP-Address:AC的源IP地址
- Service-Type:值为10(Call-Check)表示MAC认证
5. 安全增强与最佳实践
5.1 安全防护措施
- 防MAC地址欺骗:启用端口安全功能
[AC6605] port-security enable
[AC6605] port-security mac-address sticky
- 访客网络隔离:
[AC6605-wlan-vap-prof-guest] client isolation enable
5.2 性能优化建议
- 当终端数量超过200时,建议采用RADIUS认证减轻AC负担
- 配置MAC地址老化时间(默认300秒):
[AC6605] mac-authen timer offline-detect 600
- 启用AC负载均衡(多AC环境):
[AC6605-wlan-view] ap-group office
[AC6605-wlan-ap-group-office] load-balance enable
5.3 企业级部署方案
对于大型企业网络,推荐采用分层部署架构:
典型配置示例:
# 创建AP区域模板
[AC6605-wlan-view] ap-region id 1
[AC6605-wlan-ap-region-1] channel-mode 5g manual
[AC6605-wlan-ap-region-1] calibrate auto-channel-select enable
[AC6605-wlan-ap-region-1] quit
# 绑定AP组到区域
[AC6605-wlan-view] ap-group office
[AC6605-wlan-ap-group-office] ap-region id 1
[AC6605-wlan-ap-group-office] quit
实际项目中遇到的最典型问题是AP版本与AC不兼容,建议在部署前使用display ap-type all确认AP型号支持情况,并通过ftp或tftp方式提前升级AP版本。
 网硕互联帮助中心
网硕互联帮助中心




评论前必须登录!
注册